Esperanto's Custom RISC-V ISA Extensions for Energy-Efficient Machine Learning Applic... Jayesh Iyer - YouTube

SCAIE-V: A Scalable Open-source Interface for Flexible and Portable ISA Extensions - Andreas Koch - YouTube
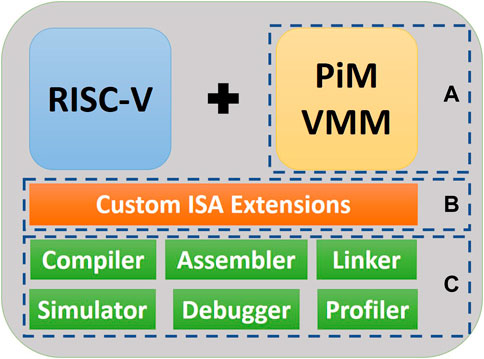
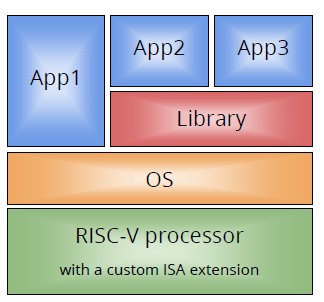
Frontiers | AI-PiM—Extending the RISC-V processor with Processing-in-Memory functional units for AI inference at the edge of IoT

InstLatX64 on Twitter: "#Intel released the 38th edition of the ISA Extensions Reference with new #SERIALIZE, #TSXLDTRK instructions and #AlderLake, #SapphireRapids infos https://t.co/NK6XAb4EWt https://t.co/QVnz4107Wl" / Twitter